You've worked hard to build trust among your employees. CEO fraud seeks to exploit that trust. And according to the FBI, CEO fraud attacks are on the rise. Not only have CEO fraud scams risen dramatically over the last decade, but these scams have cost the economy $26 billion between 2013 and 2019—with no sign of slowing down.
You don't have to become another statistic. Preventing CEO fraud can be simply training your employees to know the signs of CEO fraud so you can stop these cybercriminals in their tracks.
What is CEO fraud?
CEO fraud, also known as business email compromise (BEC), occurs when a criminal impersonates a company's CEO or other "c"-level executives (e.g., COO, CFO, CISO, etc.). However, some scam artists may attempt to impersonate customers, suppliers, or attorneys in an attempt to gain access to valuable data.
CEO scams primarily occur through fraudulent emails, though the exact goals of the scammer can vary. CEO fraud attempts to trick employees into responding by:
- Revealing sensitive information about themselves
- Sharing intellectual property with the sender
- Sending sensitive HR information
- Executing unauthorized wire transfers
- Buying gift cards to send to the CEO
What makes CEO fraud different from other types of phishing attacks? Many criminals practice what's known as "spear phishing," meaning they've performed careful research on your company ahead of time. They may have even hacked the executive's email account to send a more convincing email.
As a result, these scam artists may be surprisingly knowledgeable about your company or industry. They can "talk the talk," so to speak, which may convince employees to readily divulge sensitive information. These criminals are banking on your workers being eager to please their superiors or at least unwilling to question them.

Types of CEO fraud
CEO fraud prevention starts with awareness. Here are four of the most common types of CEO fraud attacks.
Phishing attacks
CEO fraud phishing emails are so named because they attempt to "fish" sensitive information from an employee. For instance, a hacker may disguise their email as someone from HR or your accounts payable department in an attempt to convince an employee to reveal account information or other sensitive data.
Spear phishing attacks
A spear-phishing attack is a much more focused form of phishing attack. In this method, the cybercriminal has likely spent time researching your company's website and social media sites to learn as much as possible about the business.
Then, they target an individual or department with a personalized email, often with the recipient's or top client's name.
Executive whaling
It's not just low-ranking employees who can fall victim to these attacks. Some phishing emails are meant to target a high-level executive. This is known as "executive whaling," where the criminal impersonates a senior person within the company in an attempt to harvest financial information from another company manager.
Social engineering attacks
Social engineering refers to techniques that manipulate recipients into divulging information or even sending money. Social engineering scams can look surprisingly authentic and are usually designed to manipulate you into acting without thinking.
That's all the more reason to train your team members to stay aware of common signs of social engineering to prevent a data breach.
CEO gift card scams
CEO gift card scams overlap with business email fraud, though these scams have a more specific goal in mind. Rather than ask you to reveal financial data or transfer money, they ask you to purchase a gift card. Since most e-commerce companies rely on gift card codes more than physical cards, perpetrating fraud is easier than ever.
For example, an employee might receive an email from their manager or even a high-level executive with a message something like this:
"Hey there!
I'm putting together a small surprise for the team. Can you purchase 10 Amazon gift cards and send me the code? Just use the company card, and make sure to purchase one for yourself as a thank you. Need them as soon as possible, so please respond by lunchtime today.
-Jillian"
Most employees won't stop to question the validity of the email, especially if the email domain matches the company's address—or if the email has been hacked altogether. However, once the scammer receives the gift card codes, the employee will never hear from them again.
Strategies for CEO fraud prevention
Unfortunately, you can't do much to prevent fraud attempts, but you can provide security awareness training to help your employees recognize CEO fraud attack signs. Cyber security experts recommend that you prevent CEO fraud through the SLAM method.

The SLAM method for phishing attacks is simple, and the acronym stands for:
- Sender
- Links
- Attachments
- Message
Helping your employees practice the SLAM method will make your organization less vulnerable to these types of cyber threats. Here's what to look for in each category.
Sender
Encourage employees to always check the reply-to address before emailing sensitive information. While some phishing emails are the result of scammers hacking the CEO's actual account, many other CEO fraud attacks come from email addresses that resemble legitimate email accounts.
You might spot a fraudulent email by noting a change in the email domains between a legitimate account and the email you've received. For instance, if the expected format is "yourname@tailoredmarketing.com," be on the lookout for small changes like:
"yourname@tayloredmarketing.com." The change from the "i" to a "y" in the domain name might be easy to miss when you're in a hurry, but it's a sure sign of a CEO fraud email.
Links
Train your employees to avoid clicking links unless they know where they lead. CEO fraud emails may contain hyperlinks whose text appears benign, if not helpful. But the link actually sends you to a different site altogether or downloads malicious software onto your computer without your consent (or even your knowledge).
Here's a tip: most desktop browsers let you hover over a link without clicking it. But your browser will indicate where the link actually goes. Try it yourself on the following link: Amazon.com. Employees need to understand how easy it is to mask a web address to trick them into following a malicious link.
Attachments
Attachments are another common way for scammers to infect a company computer with malware. Cybercriminals can use malware to harvest employee information or other sensitive data. Some cyber criminals can even hold your system for ransom, holding your company assets hostage unless you complete a wire transfer.
It may help to remind employees that you don't customarily send email attachments to individual employees. Allow employees to ask if you had intended to send an email attachment. That way, you can prevent malicious emails from infecting your system or stealing sensitive information.
Message
Finally, employees should check the content of the message itself. Many CEO fraud attacks rely on social engineering techniques to convince you to reveal information or transfer money to the sender. But look for grammatical or spelling mistakes that may indicate that the message didn't originate with your employer.
Be suspicious if the email requests that you reveal confidential information over company email. And if the email arrives with suspicious links or attachments, it's a good sign that you're the target of CEO fraud.

How to spot social engineering scams
Due to the prevalence of fraud, many companies hold security awareness training at least once per year. These training sessions can highlight the latest developments in CEO fraud detection and may include phishing simulations so employees can sharpen their skills to avoid business email compromise.
To that end, the following represent common ways to identify CEO fraud attack signs.
The email urges you to act quickly
Scammers want you to act quickly and not ask any questions. If you receive an urgent email from someone asking for information (or even to send money) as soon as possible, stop and think through the situation. Is this really an emergency?
If you're unsure, contact the sender directly—preferably using the information you have on file rather than simply hitting the "reply" button. Chances are that the scam artist is trying to manufacture a sense of urgency to steal money or information.
The email focuses on a secret assignment
In the earlier gift card fraud example, the scammer created a sense of urgency and kept the assignment a secret. By keeping things a secret, the scammer is preventing victims from asking questions from their co-workers.
But how often does the boss hand out "secret" assignments? Train your workers to ask questions if they receive a suspicious email about a secret project—especially if the assignment involves exchanging money or personal information.
The email offers a reward
Another clear sign of CEO fraud is that the sender offers a reward for completing the task or acting quickly.
For instance, the scammer might promise a gift card if you complete a quick survey, send money, or send them the gift card security code or other details. But it's rare for CEOs and managers to offer individualized rewards like this. Employees should be quick to spot these sorts of "prizes" for what they really are: a form of CEO fraud.
The email requests a change from standard procedures
Some CEO fraud emails will change the standard procedures in a way that benefits the scam artist.
For example, if you work with foreign suppliers, you may have an ongoing wire transfer relationship. A scam artist may contact you to change the parameters of these wire transfers, asking that you send money to a new account. If the bank accounts don't match your records, you could be looking at a CEO fraud email.
The email requests sensitive information
Another surefire giveaway is that the email requests you respond with sensitive information. For example, the writer of the CEO fraud email may be impersonating someone from HR and asking the victim to reply with personally identifying information.
The scam artist may contact another department to request company information or even customer data. Employees should always be cautious about sharing information over email, which exposes your company to data breaches.
What to do if you've been the victim of business email compromise (BEC)
Have you recently been the victim of CEO fraud? Here are some steps you can take to minimize the damage and prevent CEO fraud from happening again in the future.
Report CEO fraud to the appropriate agencies
First, you can file an FTC report and an i3C report. That way, these agencies will be aware of the fraudulent activity. The Federal Trade Commission maintains an online database, and by identifying trends and patterns, they can advise companies on how to prevent CEO fraud in the future.
File a chargeback with your credit card company
If your company has been the victim of a gift card scam, then contact your credit card provider to request a chargeback. Depending on your credit card provider, you may be able to reclaim some of the money you lost from the scam.
Institute a security awareness training policy
For optimum scam protection, institute a company-wide cyber security policy. This policy should institute training and protocols for responding to cyberattack events. While your company may have a dedicated cyber security team, other employees must be able to recognize common forms of email fraud and prevent cyberattacks.
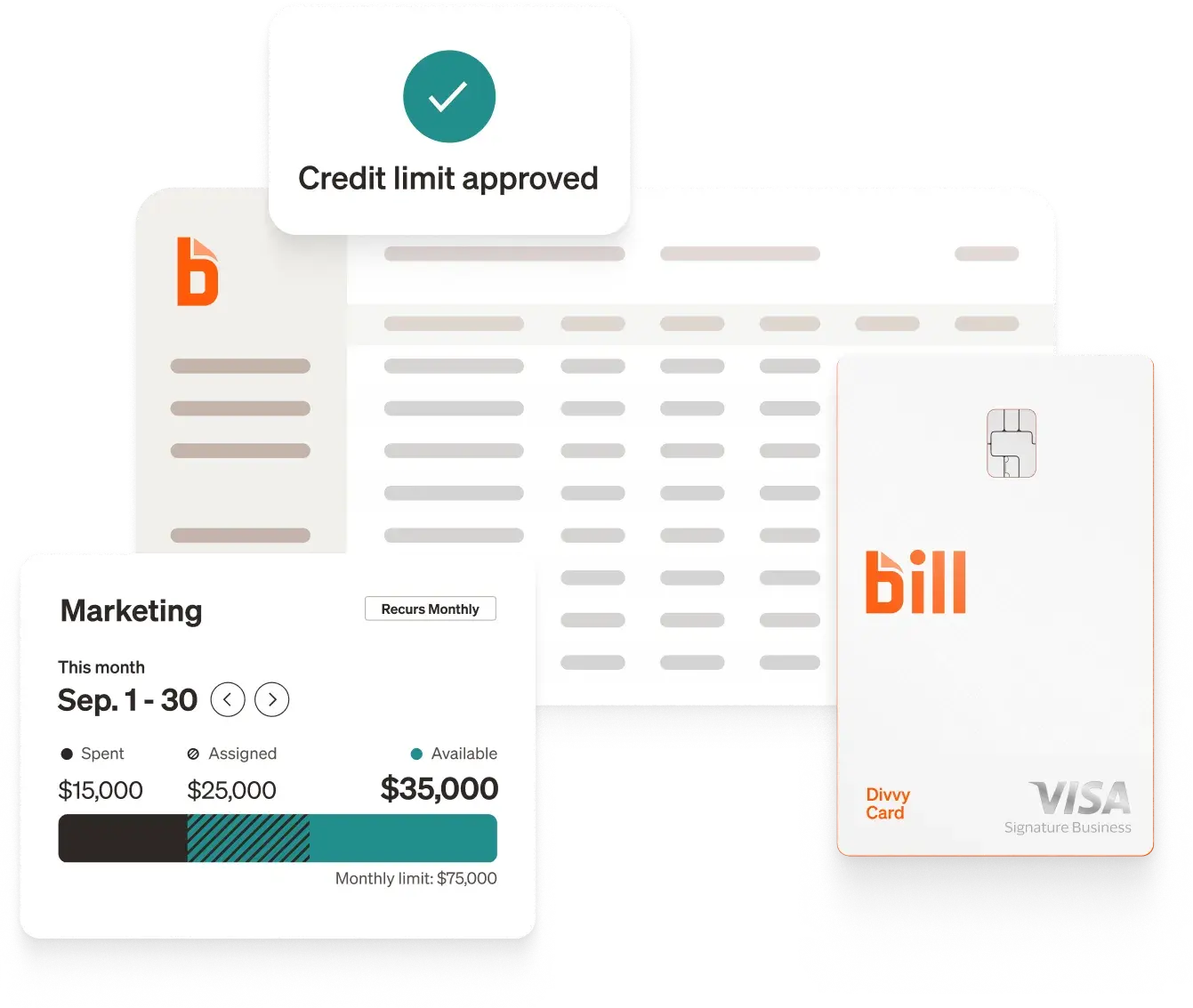
Don't just protect your business—transform it
Here's a bonus tip: use the right tools to prevent business email compromise from derailing your business. BILL has you covered. We offer advanced security features, including:
- Multi-factor authentication
- Face and touch logins
- Secure data centers
- Fraud prevention tools
Additionally, BILL offers advanced automation tools that can streamline your core business processes, all without compromising your company's security. Want to learn more? Visit BILL's security page today to discover how to transform your business.